Google abandons Topics and FLoC

Google announced that it has decided to abandon its plan to use the new Privacy Sandbox proposal called Topics and FLoC, eliminating third-party cookies, for a function that would allow users’ browsing habits to be categorized in a list of “Topics.” But there is much more to understand about this, which is why today’s article […]
The New Generation of Cybercriminals Surprises

In an increasingly technological and digital world, it should not surprise us that advances in these technologies are quickly learned and used by young people. It is not strange to see children between the ages of 3 and 10 handling a smartphone as if they were adults. That is why the new generation of cybercriminals […]
Three WordPress Plugins are Vulnerable
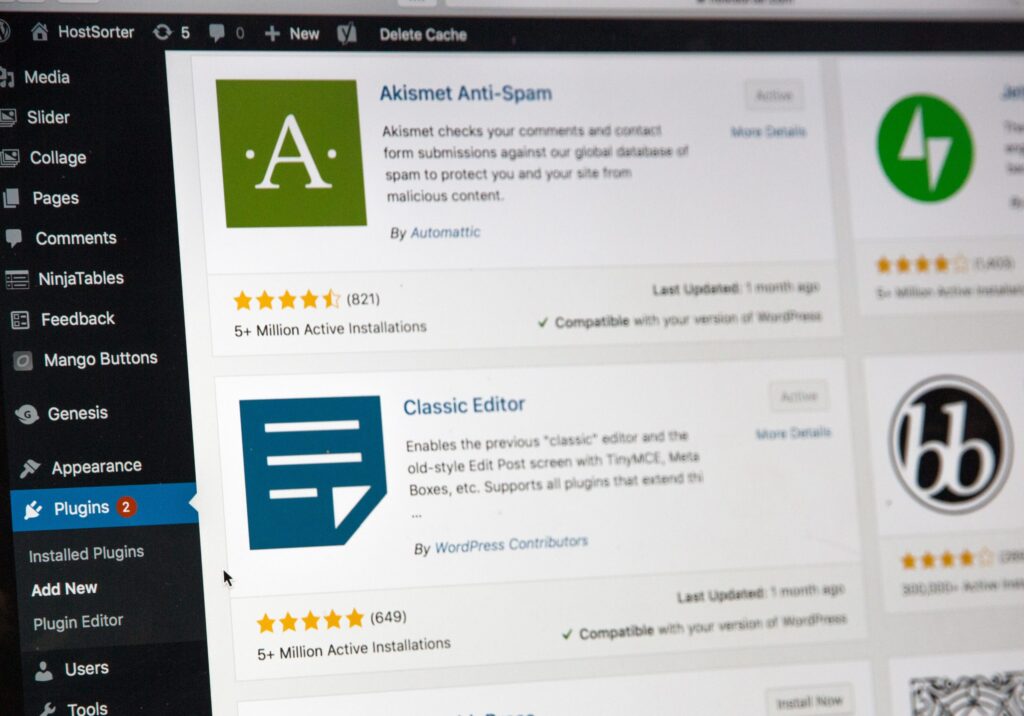
WordPress is one of the main hosting services for websites that exist. To offer the best sites, a series of plugins are used that help different functionalities depending on the nature of it. But in recent days, researchers found a security flaw in 3 of these plugins that affects the security of users who rely […]
The Use of Public Wi-Fi Networks

Being connected in today’s world is something very essential, so the use of public Wi-Fi networks has become very common. However, these networks can bring many inconveniences and even dangers from cybercriminals. In fact, they are great users of these networks, because it is difficult to track them through them. For that reason, today’s article […]
What are Cookies on Websites and Their Function?

Every time a user browses the internet and enters a new website, they’ll find a request to accept “cookies.” For convenience, most just pass these by and accept without knowing exactly what they are and what their function is. Today, we will talk precisely about these cookies on websites and how they can interfere with […]
Hackers Are Using Cloud Services to Spread Malware

Hackers are using cloud services offered by companies like Amazon and Microsoft to successfully distribute malware, such as remote access Trojans known as Nanocore, Netwire, and AsyncRAT, gaining access to systems and compromising information. Read all about this new method in this article. Read: Google Chrome is Patching Several Vulnerabilities Cloud services are the perfect […]
Google Chrome is Patching Several Vulnerabilities

The famous browser Google Chrome is presenting its first update of the year under the version 97.0.4692.71. This is caused by the discovery of 37 new vulnerabilities that put users at risk by giving access to the whole device system, not only the data from the browser itself. Keep reading the article to find out […]
T-Mobile Faced Its Second Cyberattack

T-Mobile was the victim of a cyberattack last summer, but they couldn’t end the year with good news. In December, they were again the target of cybercriminals, ready to get a hold of their customers’ data. This time, the attack was over a small number of accounts, but it only proves that the company continues […]
