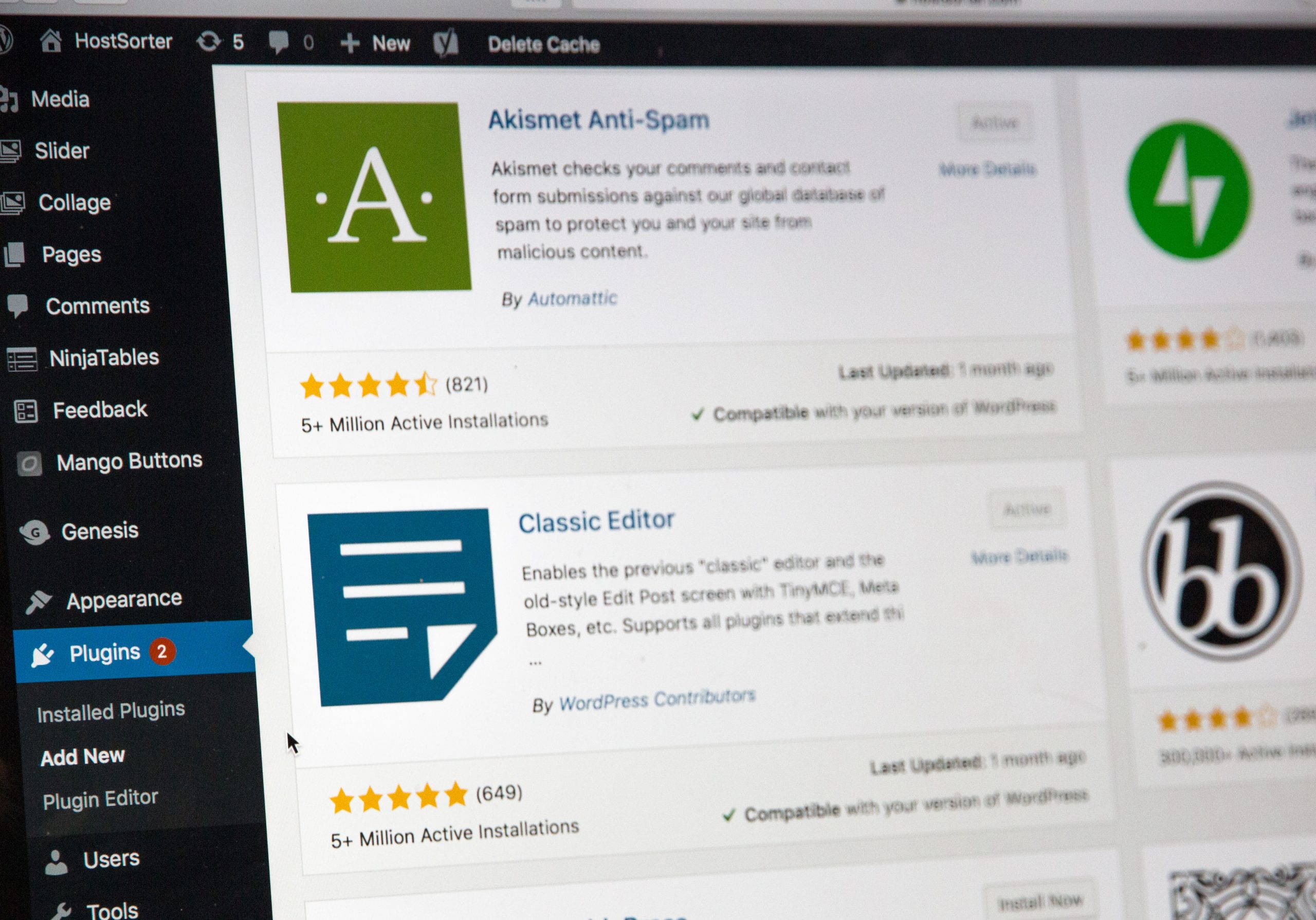
WordPress is one of the main hosting services for websites that exist. To offer the best sites, a series of plugins are used that help different functionalities depending on the nature of it. But in recent days, researchers found a security flaw in 3 of these plugins that affects the security of users who rely on them. This article will discuss the details of this flaw.
This vulnerability in WordPress affects more than 84,000 sites
The WordPress plugins that help different websites hosted on this service to work properly, can always be at risk of being affected by a vulnerability. On this occasion, 3 were affected, and it was registered under the code CVE-2022-0215. The cross-site request forgery flaw is rated 8.8 on the CVSS scale and impacts three plugins maintained by Xootix:
- Login/Signup Popup (Inline Form + Woocommerce),
- Side Cart Woocommerce (Ajax), and
- Waitlist Woocommerce (Back in stock notifier)
“This flaw made it possible for an attacker to update arbitrary site options on a vulnerable site, provided they could trick a site’s administrator into performing an action, such as clicking on a link,” WordPress security company Wordfence stated in a report.
The cross-site request forgery is also known as a one-click attack; its form of attack is simple: an authenticated user is tricked into making a well-crafted web request. Everything gets complicated if the user has administrator permissions since this request comprises the entire website.
Details of the vulnerability in WordPress plugins
The vulnerability starts in a lack of validation when processing Ajax requests. This way, the attacker changes the option that any user can register (“users_can_register”) to “true” and sets the configuration to default to all who register become automatically administrators (“default_role”), which gives complete control over the site.
Login/Signup Popup is installed on more than 20,000 sites, while Side Cart Woocommerce and Waitlist Woocommerce have been installed on more than 4,000 and 60,000 websites, respectively. It is not the first time that WordPress plugins have been attacked; they are the perfect door to take control of vulnerable sites. That is why WordPress has always been alert and tries to keep its own, and third-party plugins, updated to offer the best security to users. Keep in touch with our blog to read the latest news and innovations in the cybersecurity world.
Facebook: Eagle Tech Corp
Instagram: @eagletech_corp
Twitter: @eagletechcorp
LinkedIn: Eagle Tech
YouTube: Eagle Tech Corp




